By Adam Coreil
My parents always told me, “It’s not what you say, it’s how you say it,” and “Mean what you say and say what you mean.” These are universal principles to communicate effectively, regardless of audience or subject. These concepts apply in cybersecurity and in communicating effectively, succinctly, and in the most impactful way. However, communication around cybersecurity issues can be challenging.
Why is there a Need for Cybersecurity Technical Communicators?
Among many, many things that occurred during the unprecedented year that was 2020 (only last year!), organizations across the world were breached by the SolarWinds cyberattack. Over 18,000 of the 300,000-plus SolarWinds customers of network software were affected, including the United States (U.S.) Treasury and U.S. Commerce Department, National Institute of Health, State Department, and Department of Homeland Security, as of the writing of this article (Jankowicz and Davis, 2020). The need for organizations to clearly communicate cybersecurity threats, analyses, and cybersecurity concepts in a meaningful way is critical, now more than ever, to facilitate knowledge sharing across industries, governments, and borders.
Challenges
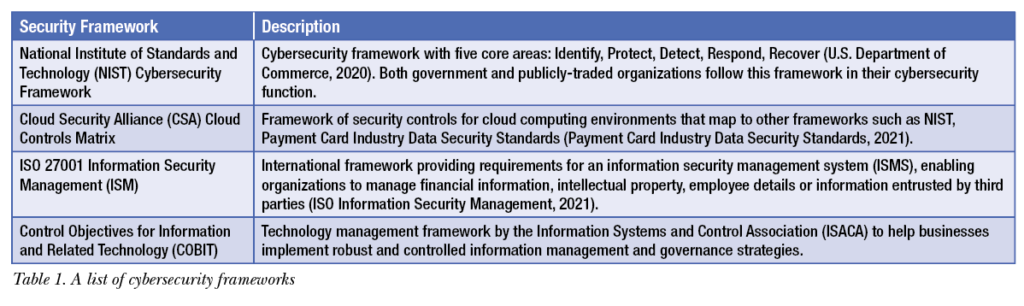
Cybersecurity departments have consistently struggled to concisely and effectively communicate cybersecurity risks, standards, and guidance. This inability has led to confusion, inconsistent security practices, and varying levels of cyber risk management. This phenomenon is not due to lack of cyber global standards and regulations! These standards and regulations include, and are not limited to, the list in Table 1.
Cybersecurity-focused technical communicators have a distinctive opportunity to bridge the communication gap in the following ways:
- Enabling consistent application of security requirements
- Providing documentation that supports treatment of cyber risks
- Authoring support procedures for security operations
Increasingly, cybersecurity is the topic of corporate board meetings and committee focus areas. Demand for clear security awareness and education is key to inform users across the enterprise. Since the COVID-19 pandemic began in 2020, one side effect has been an increase in breaches and hacks from mobile and internet of things (IOT) devices such as household appliances and company devices, including sensors for manufacturing, energy generation, and distribution systems (Sobers, 2021). Additionally, increasing data privacy and protection requirements further necessitate expertise of technical communicators focused on cybersecurity compliance requirements. According to Rob Sobers, a software engineer specializing in web security at Varonis, 95% of cybersecurity breaches are caused by human error. Technical communication professionals who focus on cybersecurity initiatives—projects, processes, and compliance—can add needed clarity to cybersecurity documentation and communications, discussed in the next section.
 Security Standards and Procedures
Security Standards and Procedures
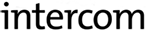
Operational security policies and procedures must be meaningful, easy to understand, and useful for an organization to operate. Security standards must be documented and regularly updated across the organization’s technology infrastructure to ensure compliance to laws and regulations. Table 2 outlines cybersecurity areas where mature security documentation could add value to compliance efforts.
Cyber Education and Security Awareness
Effective security awareness communication must be consistent and easily digestible to equip employees to make good cybersecurity choices; technical communicators are the key to this form of clear communication. According to Allison Johnson, CISO at XEROX (Sparapani, 2017), security departments need to speak in risk terms across the enterprise. One way organizations can achieve effective security and risk communication is through a strong technical communicator who has the capability to bridge technical security and business needs. Because attackers often use social engineering techniques to gain access to protected corporate information, effective security awareness training is a critical success factor. According to the 2020 Verizon Data Breach Investigations Report, cyberattackers are becoming “increasingly efficient and lean more toward attacks such as phishing.” This is a type of social engineering that uses malicious emails designed to confuse the target user and creates a sense of urgency to get them to act by opening a malicious attachment, clicking on a link, or take a more egregious action such as changing payment to a customer or vendor. Nearly 40% of malware incidents in 2020 were from email with an embedded link or attachment, according to Verizon.
Application Development: Cybersecurity in the Design
Application development teams are tasked with creating applications that enable business needs. Technical communicators can effectively translate those needs into clearly documented requirements and design specifications. Moreover, technical communicators who focus on cybersecurity and who participate on product development teams have an opportunity to ensure that product development teams incorporate cybersecurity controls throughout product development.
Although development operations (DevOps) and development security operations (DevSecOps) are relatively new terms, they are the practices of bringing together the disciplines of development, operations, and security in a more collaborative, consistent manner. The effect of good DevOps and DevSecOps in application development is shorter development iterations, along with improved flexibility, efficiency, and competitive edge (OpenSource, 2021). Agility and flexibility in today’s development practices are key to meeting the demands of business goals and customer outcomes. Application design and functional documentation approaches must also shift to approaches that are flexible to keep pace with DevOps and SecDevOps.
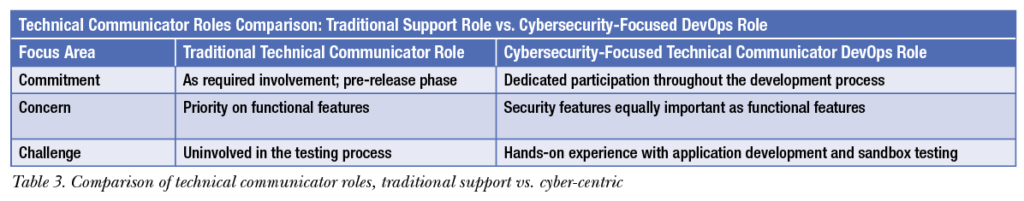
Table 3 outlines the traditional technical communicator role in a traditional support role versus a cybersecurity-centric role.
Summary
Communication and documentation accuracy, clarity, and completeness are essential for good cybersecurity. As this article outlined, the need for expertise in cybersecurity threats, control frameworks, and regulations are vital for organizations to maintain effectiveness of application documentation, meaningful educational awareness communications, and sound practical understanding of cybersecurity practices and compliance regulations. The need for cybersecurity technical communicators will continue to grow as long as humans continue to be the biggest cyber risk.

ADAM COREIL (adam.coreil@cbre.com) is a cybersecurity professional with more than 20 years’ experience in technology governance and risk. He is a Certified Information Systems Security Professional (CISSP) and Certified Information Security Manager (CISM). Adam began his career in risk consulting at Deloitte where he gained cross-industry experience in technology solutions. Outside of work, Adam enjoys research, running, and time with family.
REFERENCES
International Organization for Standardization. 2021. “ISO Information Security Management.” Accessed 21 May 2021. https://www.iso.org/isoiec-27001-information-security.html.
Jankowicz, Mia, and Davis, Charles. 2020. “These Big Firms and U.S. Agencies All Use Software from the Company Breached in a Massive Hack Being Blamed on Russia.” Business Insider. Accessed 21 May 2021. https://www.businessinsider.com/list-of-companies-agencies-at-risk-after-solarwinds-hack-2020-12.
NIST. 2020. “NIST Risk Management Framework.” Accessed 21 May 2021. https://csrc.nist.gov/projects/risk-management/detailed-overview.
OpenSource. 2021. “What is DevOps?” Accessed 21 May 2021. https://opensource.com/resources/devops?intcmp=7013a00000263HlAAI.
PCI Security Standards Council. 2021. “Payment Card Industry Data Security Standards.” Accessed 21 May 2021. https://www.pcisecuritystandards.org.
Sobers, Rob. 2021. “134 Cybersecurity Statistics and Trends for 2021.” Varonis. Accessed 21 May 2021. https://www.varonis.com/blog/cybersecurity-statistics/.
Sparapani, Jason. 2017. “Xerox CISO: Cybersecurity is ‘Enabler’ For Innovative Tech.” TechTarget. Accessed 21 May 2021. https://searchcio.techtarget.com/video/Xerox-CISO-Cybersecurity-is-enabler-for-innovative-tech?_gl=1*cazgl*_ga*MTEzMjQ2Mzc2OS4xNjEzODU2MDMz*_ga_RRBYR9CGB9*MTYx-Mzg1NjAzMi4xLjAuMTYxMzg1NjAzMi4w&_ga=2.181279588.233816123.1613856033-1132463769.1613856033.
U.S. Department of Health & Human Services. 2021. “Summary of the HIPAA Privacy Rule.” Accessed 21 May 2021. https://www.hhs.gov/hipaa/for-professionals/privacy/laws-regulations/index.html#:~:text=The%20Privacy%20Rule%20protects%20all,health%20information%20(PHI).%22.
U.S. Department of Commerce. 2020. National Institute of Standards & Technology Cybersecurity Framework. Accessed 21 May 2021. https://www.nist.gov/cyberframework.