Category: Talking Usability

Talking Usability: Trust is Key to Winning User Acceptance
People are skeptical of change because they do not trust that the change will be beneficial
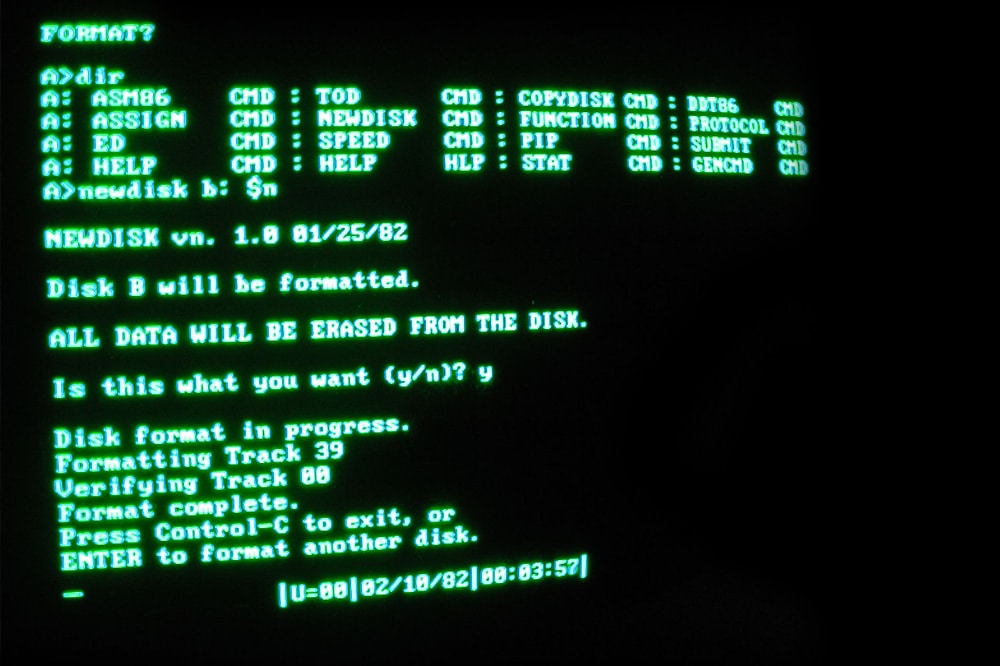
Talking Usability: Legacy Systems and Their Impact on Users
Users generally do not care if a system is based on an old method, technology, or computer system. Users want reliable, dependable, and secure systems. Every year, IT managers meet to discuss how to replace legacy systems. As long as these systems adequately serve the organization and the budget does not allow for modernization, they are likely to remain unchanged. IT managers need to weigh the cost and risk of keeping legacy systems, such as end user support, training, documentation, and security.

Talking Usability: Don’t Trade Security for Usability on Your Smartphone
The convenience of mobility and an infinite number of mobile applications has changed the way we use a smartphone. Consequently, we store a lot of personal information on a smartphone such as email addresses, passwords, travel information, driver’s licenses, personal identification numbers, boarding passes, credit card numbers, bank account numbers, telephone numbers, and photographs. Would you want someone to break into your smartphone and retrieve the data for nefarious use? Obviously not, but nevertheless, few of us take the same precautions to protect our smartphone that we do for our laptop or desktop because we do not want to complicate its use
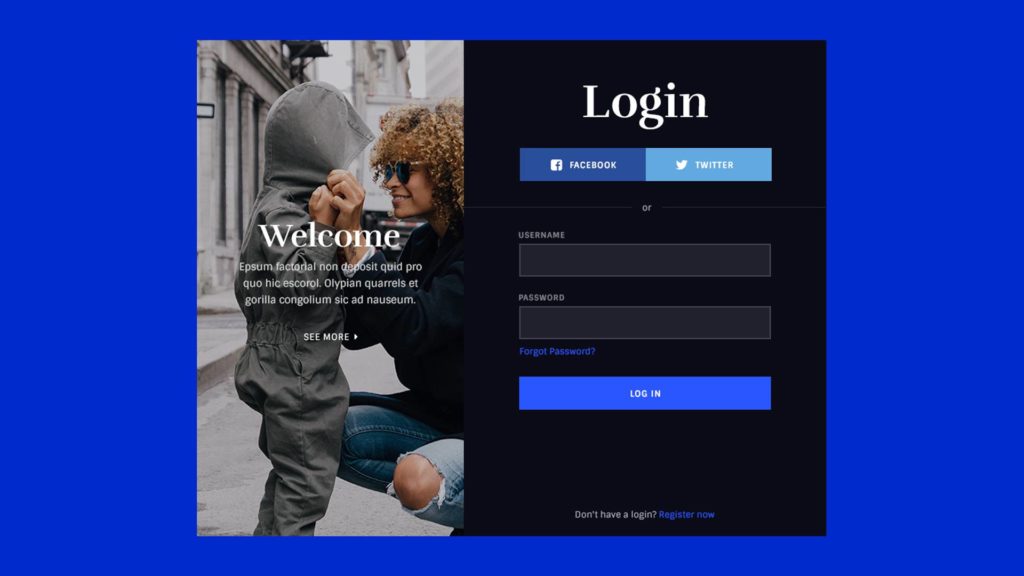
Talking Usability: There’s No Such Thing as a User-Friendly Password
Passwords are required for all types of online activity to authenticate the user. One thing is certain: until technology provides a better solution to passwords, we must learn to create strong passwords and remember them in order to safeguard our personal data from hackers.
Talking Usability: Lessons Learned About PDF Accessibility
Many of us hold this assumption to be true—we can convert text documents into Accessibility-compliant Portable Document Format (PDF) documents by saving them as PDF. Any desktop publishing tool can create PDF files using “Save as Adobe PDF”; however, the PDF files it creates are not always Accessibility-compliant for screen readers.
Talking Usability: Technology is Changing, But Not At the Workplace
We, as savvy consumers, must have the latest technology. We buy the newest smartphone because it has something that our current smartphone doesn’t have. We download the latest Web applications because we believe they will empower us. Our Internet connection is as fast as the provider can deliver because we have no patience to wait for anything. Most importantly, we make the time to learn because we want to become savvy users. Our workplace; however, is another story.
Talking Usability: My Father’s Typewriter
My father typed all his correspondence on a manual (non-electric) typewriter. The ink on the typewriter ribbon was so worn out that the text on the paper was barely legible. Office supply stores stopped selling manual typewriter ribbon because electric Read more
Talking Usability: Do They Have Your Computer for Ransom?
You might try to click away only to discover that your browser is locked. You might reboot your PC only to discover that the banner is still there. Out of desperation you call the Help Desk listed on the banner, the customer support technician promises to remove the virus for $300, and promises to run a virus scanner to remove the virus and update your security software—what a bargain, you think. You provide your credit card number, and the customer support technician tells you where on your PC to run a script and after a few minutes the banner is gone. You are so happy that you dance with joy. When it’s over, you contact the Better Business Bureau about this Windows Support company and discover that is it not accredited by Microsoft or Apple to provide Windows or Mac support.
Talking Usability: Inattentive Behavior and Smartphones
One day while driving, I was looking down at my smartphone to tap the numbers to make a phone call. My attention to the road was only interrupted for a few seconds. When I looked up, I was too close for comfort to the car in front of me. I slowed down to let the car in front of me gain more distance. I was lucky, but the situation made me think about how smartphones affects our attention.