By David Dick | STC Fellow
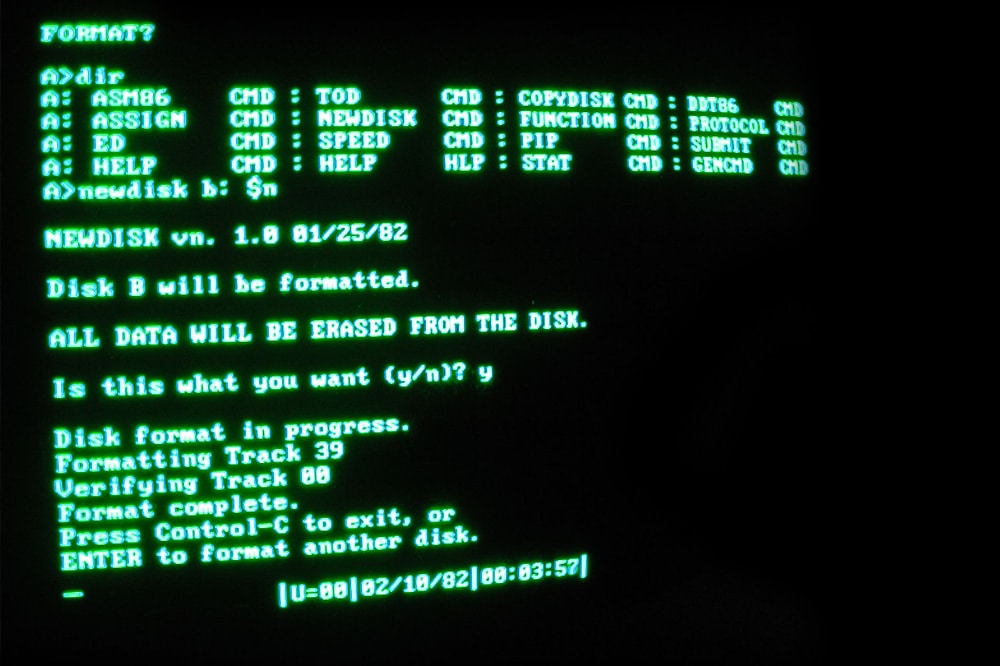
Users generally do not care if a system is based on an old method, technology, or computer system. Users want reliable, dependable, and secure systems. Every year, IT managers meet to discuss how to replace legacy systems. As long as these systems adequately serve the organization and the budget does not allow for modernization, they are likely to remain unchanged. IT managers need to weigh the cost and risk of keeping legacy systems, such as end user support, training, documentation, and security.
Employees that provide end user support of legacy systems must be retained, because they are familiar with users’ frequently asked questions and know how to work around common problems. Unfortunately, whenever they are out of the office, their absence creates a backlog of help desk tickets that cannot be answered until they return, preventing users from performing their work. Another dilemma is that when these employees inevitably move on or retire, they take their knowledge with them. Service companies might be able to fill the gap, but ultimately they also struggle to find experts with the right skills.
Training for new users on a legacy system is often nonexistent, because the only people capable of providing the training are the same people that provide end user support. Even if there is a user guide or tutorial, users still prefer to call the help desk. Often, the help desk will perform the task because it’s easier than explaining to a user how to do it. IT managers need to be aware that a lack of training is creating additional work for the help desk.
Documentation on the design of legacy systems might exist, but it likely hasn't been updated. Documentation is always needed whenever new system administrators, stakeholders, and IT managers want to know how the system processes data, generates reports, connects to the network, and interfaces with other systems. IT managers can create the unrealistic expectation that system administrators and staff maintain documentation, but neither of these groups have the time for such a daunting task.
If a legacy system is created on a platform that a vendor no longer supports, a third party vendor must be contracted to support it. However, operating systems without security patches are prone to hacking, viruses, and other malicious attacks. If it’s not possible to update security patches, the only option to protect the system is isolating it from the rest of the enterprise, which might not be practical if it interfaces with other systems. The value that system security auditors provide is conducting network scans to identify system vulnerabilities and bringing them to the attention of system owners.
All things considered, legacy systems provide critical services to organizations, and replacing them isn't easy. That’s why IT managers need to be aware of the people who ensure those systems are up and running, and the impact those systems have on users.