By Jessica Behles
Cybersecurity is a shared responsibility. Whether the CEO of a Fortune 500 company, an employee connecting remotely to the company network, a teacher using Zoom to conduct classes, or a parent simply trying to keep the kids safe, we must all do our part to make the Internet a safer place.
Indeed, cybersecurity should be a priority for anyone using internet-connected technology. For a technical communicator working with technology every day, both at work and in the home, a basic education in cybersecurity not only keeps you, your family, and your employer safe, but may also open up new opportunities.
When I stumbled into cybersecurity in 2013, I knew very little about the field despite being fairly technologically literate. I understood basic internet security, but I had much to learn before I could fulfill my duties. Furthermore, there is an overwhelming amount of information out there, and it is constantly changing. I muddled through, but I wish I’d had some guidance beyond the company’s basic awareness training.
Because of these challenges, I created this “quick start guide” to help you hit the ground running with cybersecurity, whether you are an everyday user of technology or considering a career in the field.
This article is broken into beginner, intermediate, and advanced sections. Each section contains a list of resources you can use as a starting point for your education and research. “Beginner” contains the most basic information, similar to what a company might offer in its training and awareness program. “Intermediate” is for those who are comfortable with technology and wish to go beyond the basics to protect themselves against additional threats. “Advanced” is intended for those who are interested in pursuing a career in cybersecurity or simply want to know even more about the field.
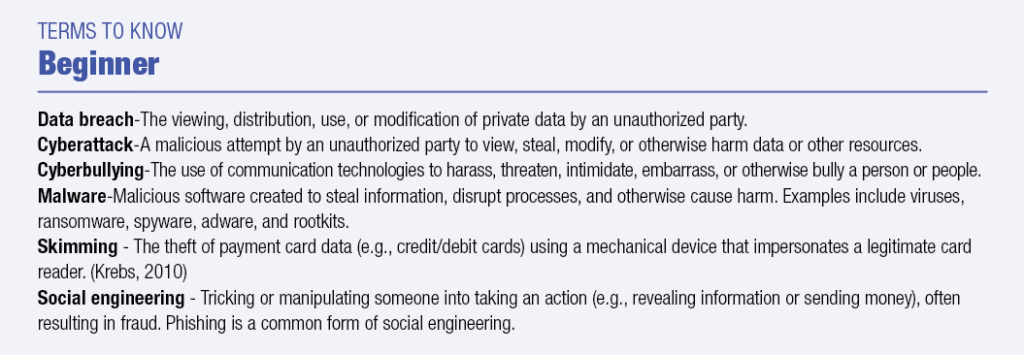
Beginner
The resources and information in this section are similar to what a company with a robust security awareness program would provide to its employees. Because not all companies offer such programs, this information should not be neglected, even though it might be considered basic knowledge. Topics covered by the resources listed below include username and password hygiene, recognizing and avoiding social engineering, identity theft, malware, social media safety, and protecting some of the most vulnerable members of our society—such as children and seniors—online.
A good starting place to begin learning about cybersecurity is Stop. Think. Connect. (https://stopthinkconnect.org/tips-advice/general-tips-and-advice), which provides some simple, actionable tips to develop and practice good online safety habits. Check the Resources tab for tip sheets covering topics like passwords, safe online shopping, and ransomware.
A slightly more in-depth offering is the National Cyber Security Alliance’s “How to Stay Safe Online” (https://staysafeonline.org/stay-safe-online/). This site provides information about keeping your information private, securing accounts and devices, and checking privacy settings on popular devices and websites. You can also learn what to do if you become the victim of a cybercrime.
The U.S. Federal Trade Commission’s “On Guard Online” (https://www.consumer.ftc.gov/features/feature-0038-onguardonline) offers tips for keeping your personal information safe, such as using public Wi-Fi networks safely and recognizing social engineering. There are also resources for parents who want to learn to keep their children safe.
The SANS Institute—one of the largest cybersecurity research and training organizations—publishes OUCH!, a newsletter with a different security topic each month (https://www.sans.org/security-awareness-training/ouch-newsletter). Past topics have included passwords (April 2019), secure online shopping (November 2019), social media privacy (February 2020), and safe video conferencing (August 2020). Consider subscribing to ensure you don’t miss future topics.
If you are looking for more information about keeping your kids safe on the internet, CyberWise’s Online Security Hub” (https://www.cyberwise.org/online-security-hub) is a resource site for busy grownups seeking to help youth use tech safely and wisely. This site has information and resources to help parents keep their children safe online at any age. It includes basic tips and guides and has aggregated hundreds of articles about youth online security from all over the internet.
Finally, for a mix of basic and more advanced information, you can visit the U.S. Cybersecurity and Infrastructure Agency’s (CISA) internet “Tips” (https://us-cert.cisa.gov/ncas/tips). This site offers a broad assortment of information spanning from basic password advice and e-mail safety to home network security and encryption.
Intermediate
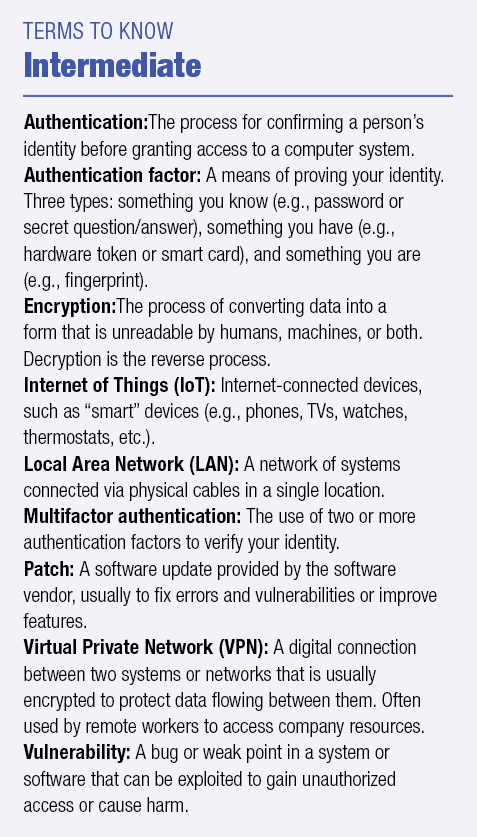
The information in this section is intended for those with a basic cybersecurity education who want to learn more about protecting themselves and others against additional threats. Topics covered by these resources include Virtual Private Networks (VPNs), mobile device security, Internet of Things (IoT) security, home network security, and encryption.
The FTC’s Online Security portal (https://www.consumer.ftc.gov/topics/online-security) includes beginner topics like recognizing scams and reducing spam emails; however, you can also learn about more advanced means to protect yourself, like securing your home wireless network, using a Virtual Private Network (VPN), safely using mobile apps, and setting up Internet cameras (e.g., webcam, online surveillance camera, etc. securely.
I mentioned the CISA’s Internet Tips website (https://us-cert.cisa.gov/ncas/tips) as a beginner resource, but it also covers topics like Denial Of Service (DoS) attacks, securing Internet of Things (IoT) devices, securing wireless networks, and threats like rootkits and botnets. Additionally, CISA offers a number of publications that cover many of these topics in greater detail.
Blogs can be a great way to learn more about cybersecurity. Two that are particularly well known and respected are Brian Krebs’ Krebs on Security (https://krebsonsecurity.com)and Bruce Schneier’s Schneier on Security (https://www.schneier.com/). While I personally prefer Krebs’ investigative journalism over Schneier’s style of aggregating and commenting on others’ articles, both authors report on cybersecurity news and topics in an approachable manner that non-experts can understand and enjoy.
Other respected blogs and cybersecurity news aggregators include Dark Reading, Zero Day (https://www.zdnet.com/blog/security/), The Hacker News (https://www.thehackernews.com), and Threatpost (https://threatpost.com/).
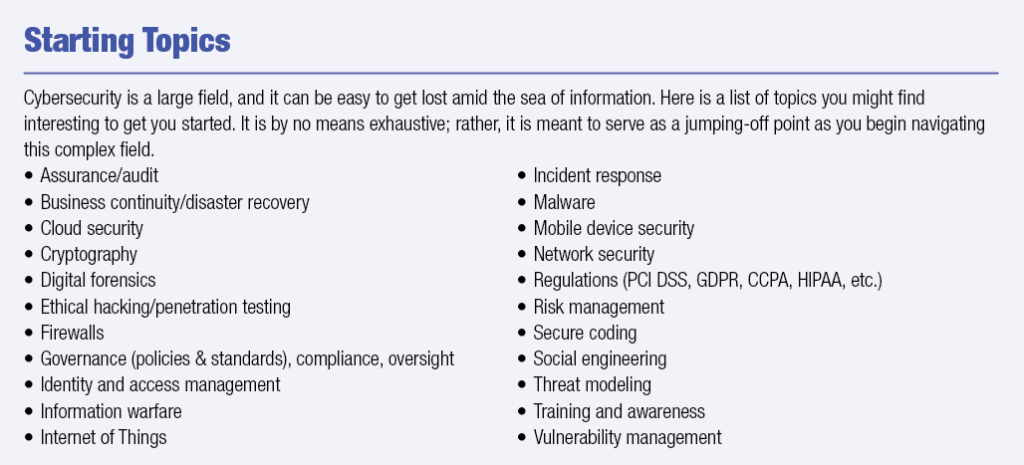
Advanced
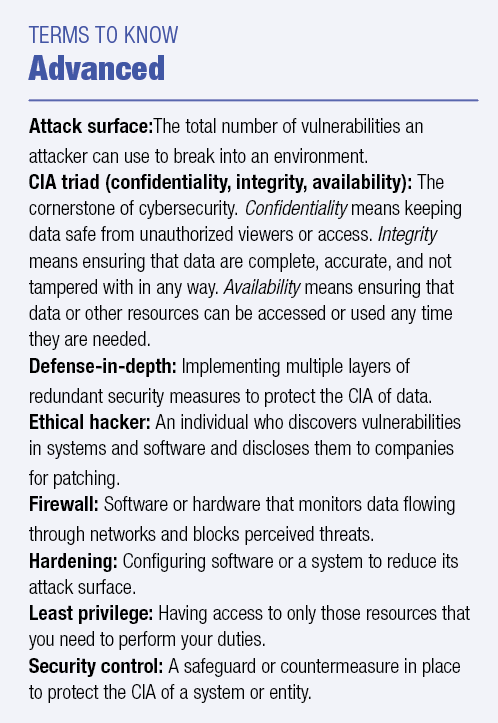 If you find cybersecurity interesting, it might be worth considering for a career. It is a dynamic, growing field that is facing a well-documented shortage of qualified workers. Furthermore, many of the greatest challenges are due to individuals, rather than technology, and the solutions to these challenges often lie in skillful communication (Flores, 2018, Whatis.com. n.d.).
If you find cybersecurity interesting, it might be worth considering for a career. It is a dynamic, growing field that is facing a well-documented shortage of qualified workers. Furthermore, many of the greatest challenges are due to individuals, rather than technology, and the solutions to these challenges often lie in skillful communication (Flores, 2018, Whatis.com. n.d.).
The resources in this category are intended for those who intend to pursue a career in cybersecurity or simply wish a more complete understanding of the field.
The SANS Reading Room (https://www.sans.org/reading-room/categories) is home to more than 3,000 white papers about various cybersecurity topics, with more being added each month.
Along with the blogs included in the Intermediate section above, Infosecurity Magazine (https://www.infosecurity-magazine.com/) and SC Magazine (https://www.scmagazine.com/) are great for expanding your knowledge and keeping abreast with news and changes within the field and threat landscape.
Anyone in cybersecurity should know about the Verizon Data Breach Investigations Report (https://enterprise.verizon.com/resources/reports/dbir/). Published each year by Verizon’s Enterprise Services division, it aggregates and analyzes data about the previous year’s data breaches to identify trends, new attack vectors, common tactics, attackers, victim profiles, and more. It is dense, but well formatted and readable, and I strongly recommend reading it every year.
If you prefer more guided training, the awesome-infosec GitHub (https://github.com/onlurking/awesome-infosec) has compiled an extensive list of training and college-level classes, many of which are free. Additionally, you can search on Coursera for free or paid cybersecurity courses (https://www.coursera.org/learn/security). Finally, Cybrary (https://www.cybrary.it/) is a training platform geared for cybersecurity professionals. It has a monthly fee after a two-day free trial; however, it does offer some free courses, many of them changing monthly.
Another approach to diving into cybersecurity is to read the regulations and best practices that companies are often required to follow. It would be impractical to list all of them here, so here is a sample of the ones you are most likely to encounter:
The Center for Internet Security (CIS) (https://www.cisecurity.org/controls/) publishes a list of the top twenty best practices that allow organizations to efficiently reduce risk in their environments.
The General Data Protection Regulation (GDPR)(https://gdpr-info.eu/) is a law that dictates how companies must protect the personal information of European Union (EU) citizens. Any company doing business with EU citizens must comply or face fines in the millions of Euros.
HIPAA-The Health Insurance Portability and Accountability Act of 1996 (https://www.hhs.gov/hipaa/index.html) dictates how protected health information (PHI) must be collected, used, and safeguarded. All organizations handling PHI are subject to this law.
The National Institute for Standards and Technology (NIST) publishes a suite of more than 200 Special Publications (SPs) that focus on information security and cybersecurity topics and best practices. I recommend starting with NIST SP 800-53 (https://csrc.nist.gov/publications/sp800) and Security and Privacy Controls for Federal Information Systems and Organizations (https://csrc.nist.gov/publications/detail/sp/800-53/rev-5/final).
NIST also produces a framework for improving critical infrastructure security. (https://www.nist.gov/cyberframework). Many organizations have adopted the Framework to guide their approaches to cybersecurity.
The Cybersecurity Maturity Model Certification (CMMC) is a program used to consistently measure cybersecurity implementation. This certification, which includes and expands on the controls in NIST SP 800-171, is required for U.S. Department of Defense contractors and subcontractors; however, many companies use this model to assess their own cybersecurity capabilities (https://www.acq.osd.mil/cmmc/).
Most financial companies are required to follow the Payment Card Industry Data Security Standard (PCI DSS) (https://www.pcisecuritystandards.org/), which focuses mainly on protecting credit card customers and other consumers of financial products.

JESSICA BEHLES (j.e.behles@gmail.com) is currently a cybersecurity technical writer for Discover Financial Services. She has a BS in Technical Communication from New Mexico Tech and an MS in Technical and Professional Communication from UW-Stout. She also holds GIAC-GISF, GIAC-GSEC, and GIAC-GSTRT certifications and is studying for her CISSP. Jessica is enjoying the weather in New Mexico with her husband, two black Labs, and a black cat who rules the household.
REFERENCES
Flores, Maria Antonieta. 2018.The Language of Cybersecurity. XML Press.
Krebs, Brian. 2010. “All About Skimmers.” Krebs on Security. Accessed 21 May 2021. https://krebsonsecurity.com/all-about-skimmers/.
PCI Security Standards Council. n.d. “PCI-DSS Glossary.” Accessed 21 May 2021. https://www.pcisecuritystandards.org/pci_security/glossary.
Whatis.com. “IT Career Management.” Accessed 21 May 2021. https://whatis.techtarget.com/.